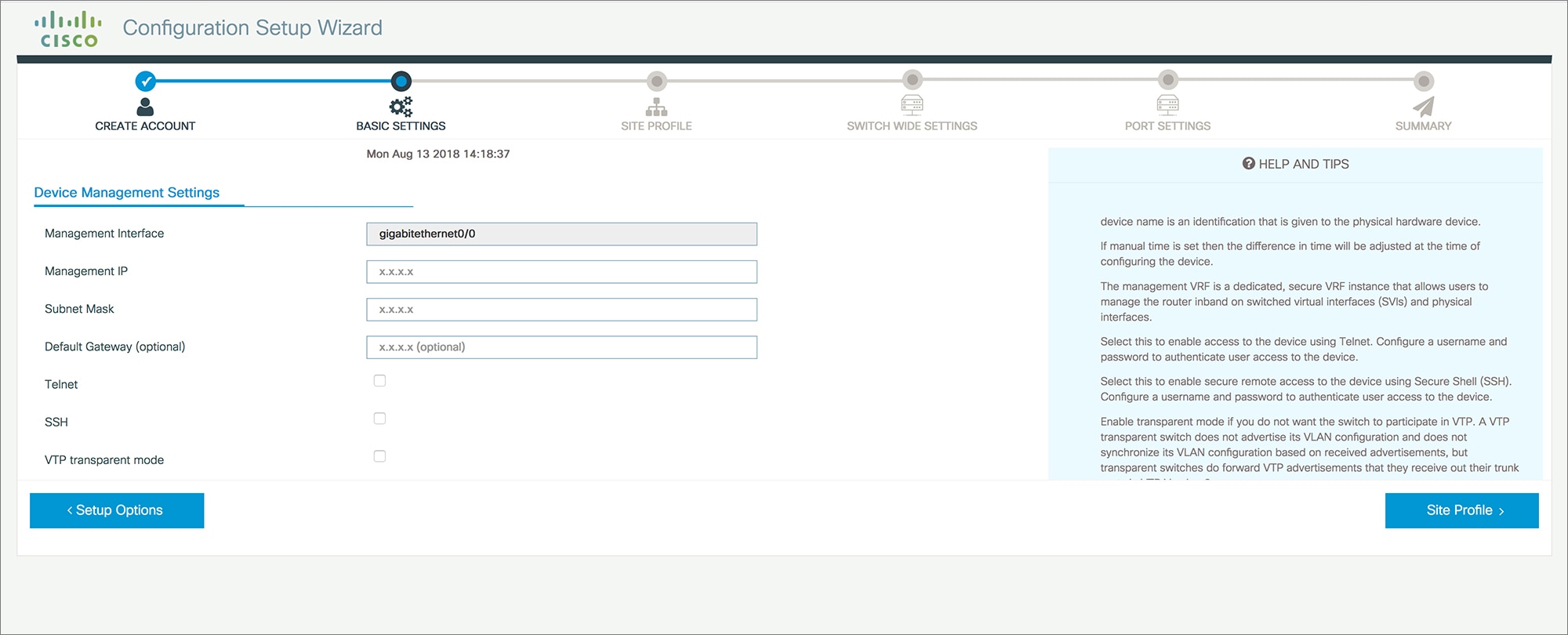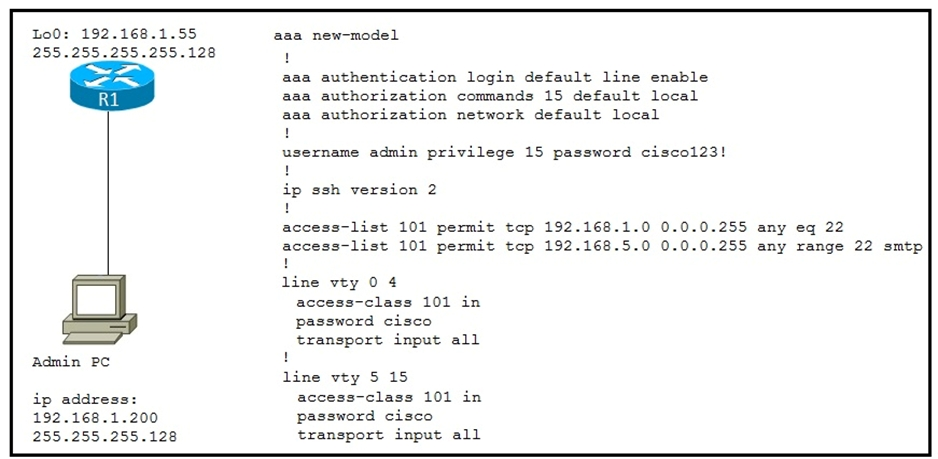
Securing Administrative Access to a Cisco Router | Securing Cisco Routers | Pearson IT Certification
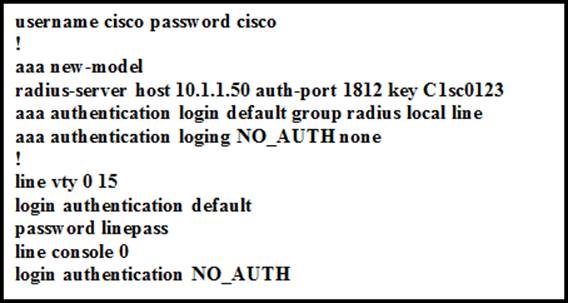
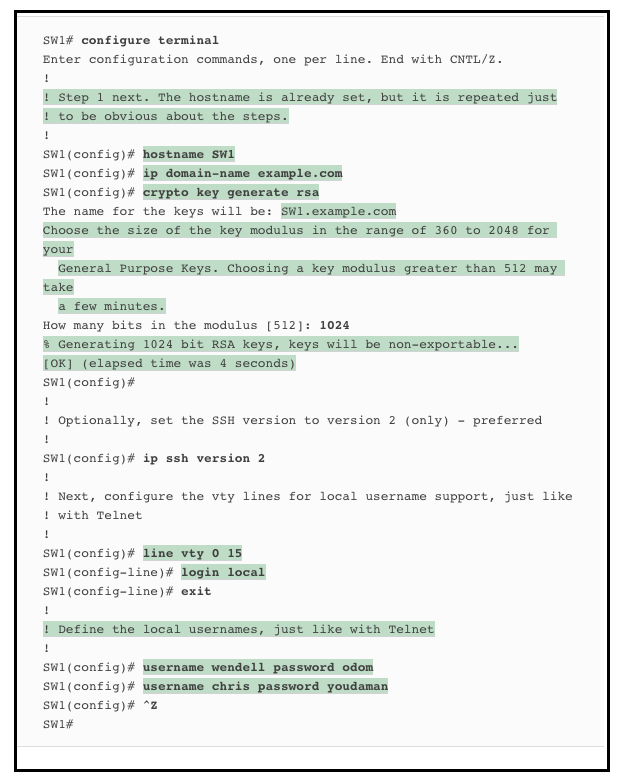
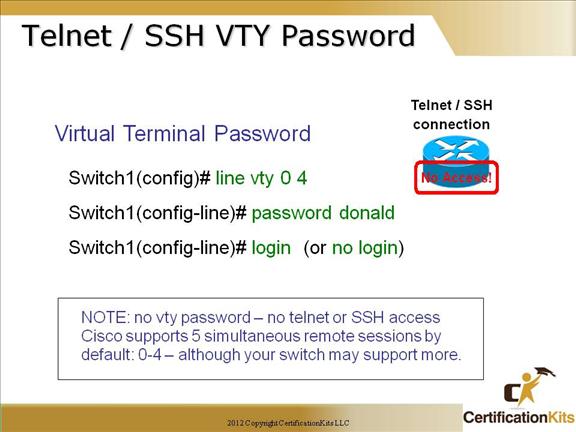
When a network administrator is attempting an SSH connection to the device, in which order does the device check the login credentials? - Exam4Training

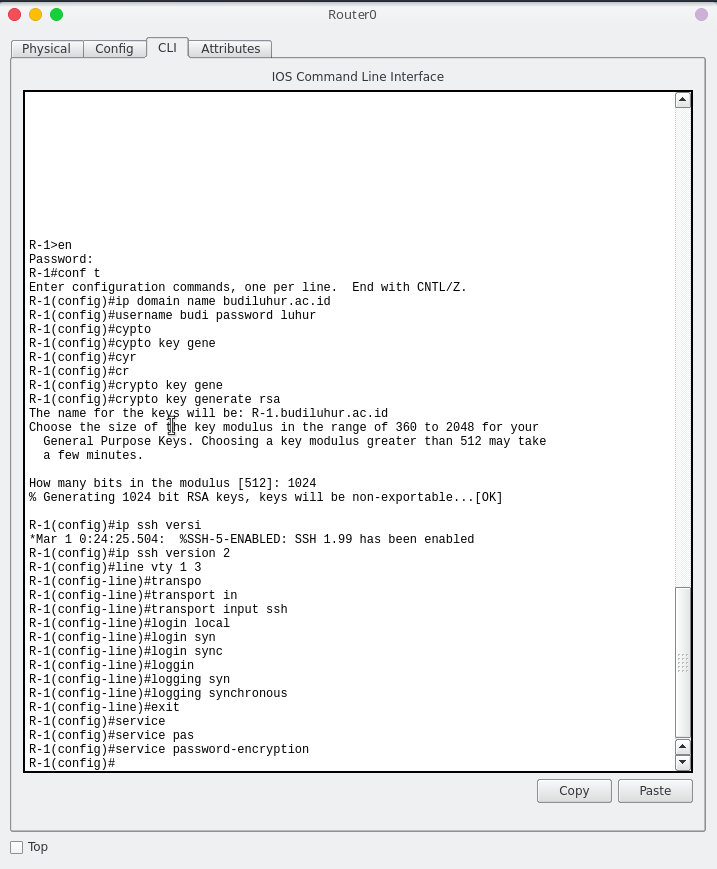
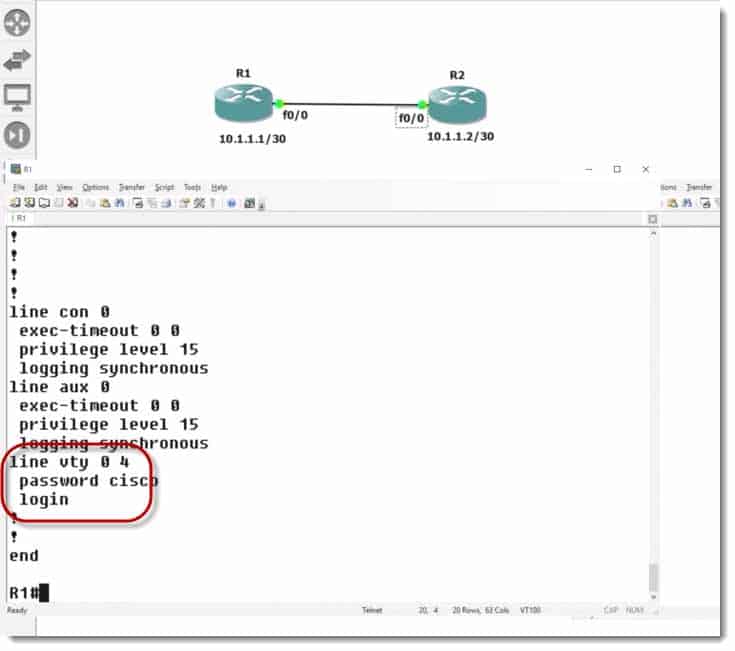
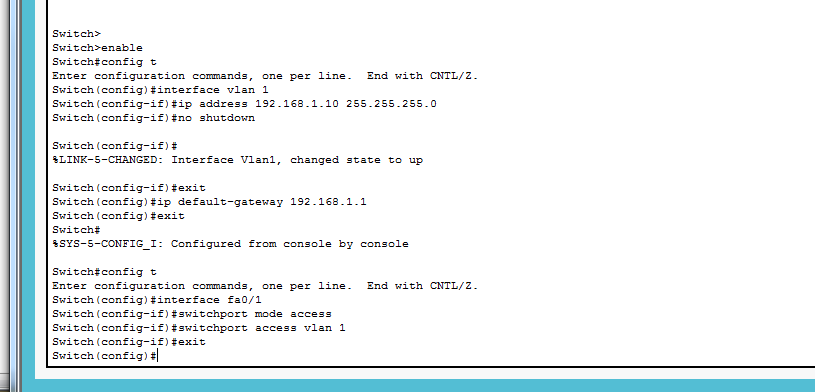
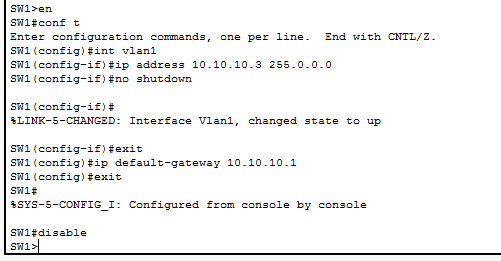
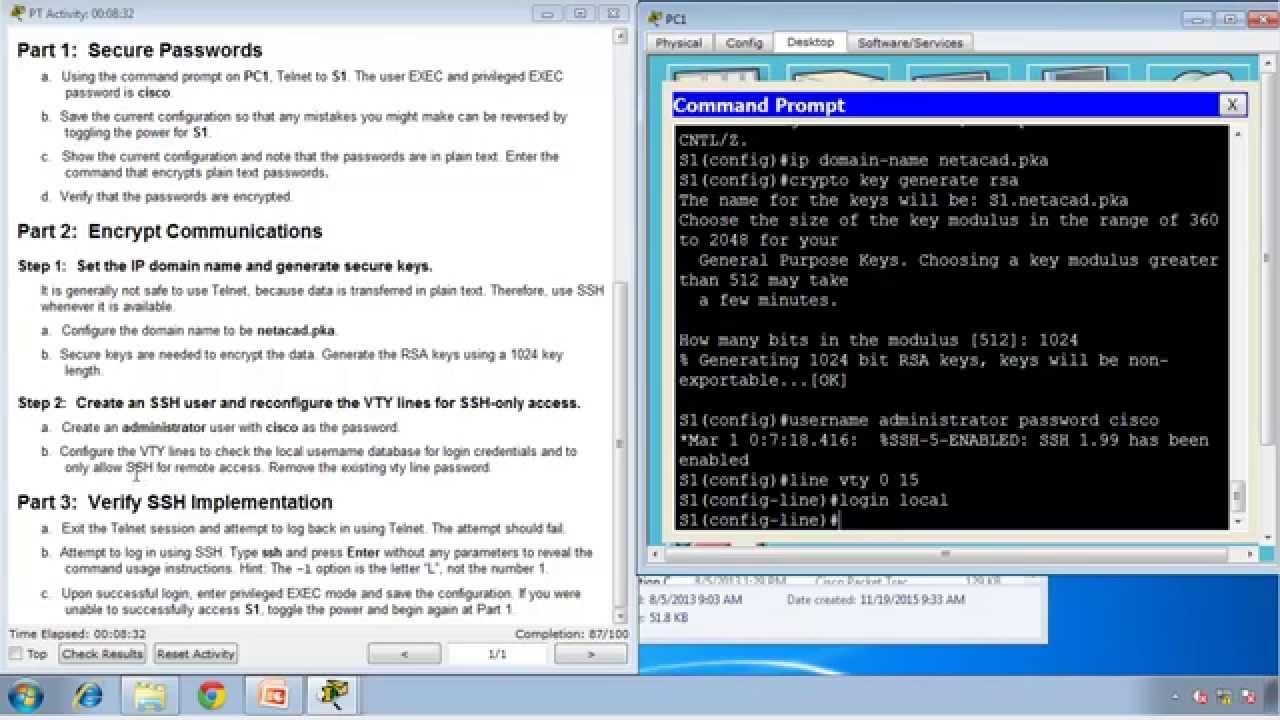
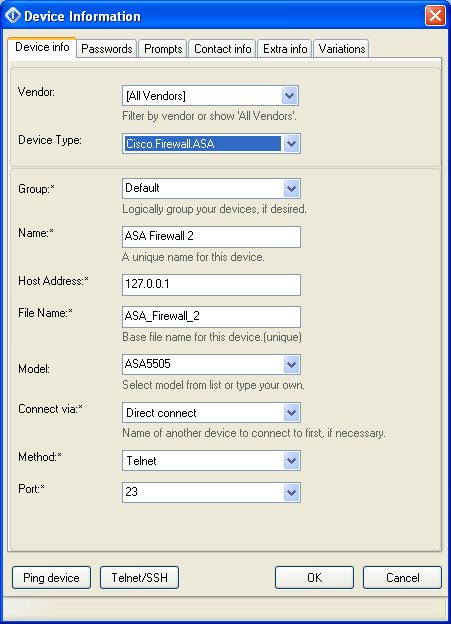
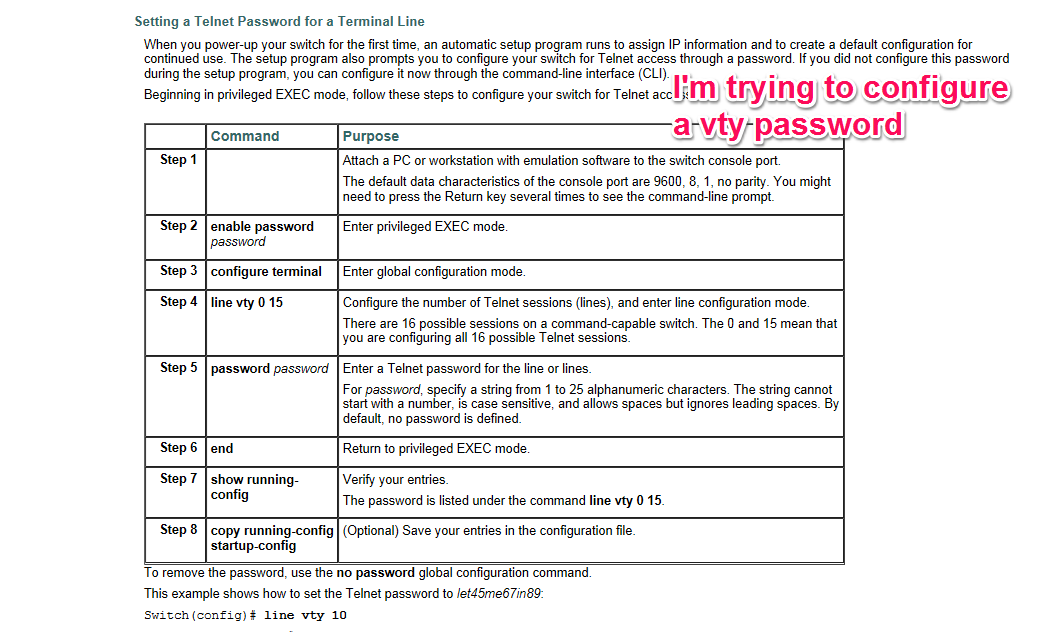
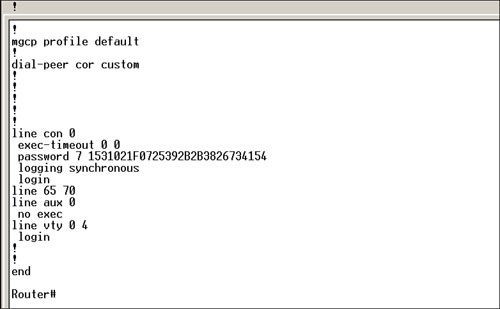
7.2.3.4 Lab - Configuring and Verifying VTY Restrictions Act 16 (1) | Ip Address | Router (Computing)

User Login Configuration - NE20E-S V800R011C10 Configuration Guide - Basic Configurations 02 - Huawei